DarkGate Malware Campaign Exploits Microsoft Windows Vulnerabilities
In mid-January 2024, a sinister cyber threat surfaced, targeting unsuspecting users through…
QNAMO: The Deceptive Cryptocurrency Trojan
In the ever-evolving landscape of cyber threats, a new menace has emerged,…
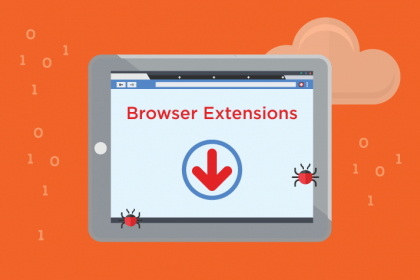
Yellow Tab Browser Hijacker: A Detailed Guide to Removal and Prevention
In today's digital landscape, where browsing the web has become an integral…
Zombi New Tab Browser Hijacker: A Comprehensive Guide
In the ever-evolving landscape of cyber threats, browser hijackers pose a significant…
Juice Finance’s Airdrop Scam: Protect Your Digital Assets
In the fast-paced world of cryptocurrency, where innovation and opportunity abound, so…
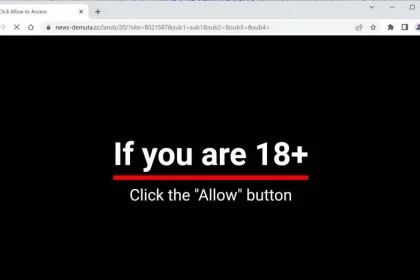
Fake Bot Check Alert: The Threat of Artistictastesnly.info
In the vast landscape of the internet, threats to cybersecurity are ever-evolving,…
Snake Infostealer: A Sophisticated Cyber Threat Targeting Facebook Users
In the ever-evolving landscape of cybersecurity threats, the emergence of the Snake…
WogRAT: The Persistent Cyber Threat Targeting Windows Systems
In the ever-evolving landscape of cybersecurity, a persistent and formidable adversary has…
Runicforgecrafter.com: Beware of Deceptive Push Notification Scams
In the ever-evolving landscape of cybersecurity threats, malicious actors continually devise new…
Payuransom Ransomware: A Threat Analysis and Removal Guide
In the ever-evolving landscape of cyber threats, ransomware remains one of the…