DroidBot RAT (Remote Access Trojan): A Guide to Understanding, Removing, and Preventing Infection
What is DroidBot? DroidBot, also known as DroidBot RAT (Remote Access Trojan),…
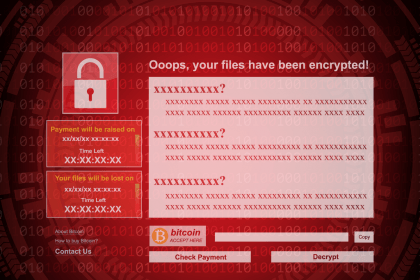
AllCiphered Ransomware: A Detailed Overview and Removal Guide
AllCiphered is a variant of the notorious MedusaLocker ransomware family, a type…
Zephyr Miner: A Cryptocurrency Miner Malware Threat
Cryptocurrency miners, also known as cryptominers, are increasingly becoming a significant cybersecurity…
SMOK Ransomware: A Dangerous Crypto Virus Threat
SMOK is a type of ransomware that encrypts files on the victim’s…
Imploder Ransomware: A Growing Threat to Your Files
Imploder is a newly discovered ransomware that has raised concern among cybersecurity…
Pro Video Downloader: A Dangerous Adware Threat
Pro Video Downloader is an extension promoted as a convenient tool for…
ViT Ransomware: How to Detect, Remove, and Protect Against This Dangerous Threat
ViT ransomware, part of the notorious Xorist family, is a highly destructive…
Revive Ransomware: How to Remove It and Prevent Future Infections
Ransomware remains one of the most alarming forms of malware, targeting both…
MAGA Ransomware: A Comprehensive Guide to Detection, Removal, and Prevention
Ransomware attacks are among the most devastating forms of cyber threats, capable…