Fedapush.net has emerged as a potent malware, causing significant damage to unsuspecting users worldwide. This insidious threat operates stealthily, exploiting vulnerabilities to infiltrate systems, compromising sensitive data, and disrupting normal operations. Understanding its actions, consequences, and effective removal techniques is crucial in safeguarding against its detrimental effects.
Actions and Consequences of Fedapush.net
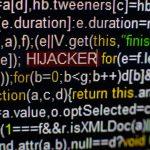
Fedapush.net operates as a malicious software program, primarily propagated through deceptive means such as phishing emails, compromised websites, or bundled with freeware applications. Once it gains access to a system, it establishes persistence by modifying critical system settings and registry entries. This enables it to execute various malicious activities, including:
- Information Theft: Fedapush.net is designed to harvest sensitive information such as login credentials, financial data, and personal details, which can be exploited for identity theft or financial fraud.
- Browser Hijacking: It manipulates browser settings, redirecting users to malicious websites, injecting unwanted advertisements, and altering search results to promote dubious products or services.
- System Instability: The malware consumes system resources, leading to sluggish performance, frequent crashes, and unresponsive behavior, ultimately compromising the overall stability of the system.
Detection and Similar Threats
Fedapush.net may be detected by various security software under different names, including but not limited to:
- Trojan:Win32/Fedapush
- PUA:Win32/Fedapush
- Adware.Fedapush
- Trojan.GenericKD
- HackTool:Win32/Fedapush
Similar threats include adware, spyware, and trojans like:
- Reveton
- Zlob
- Conduit
- Kovter
- CoinMiner
Fedapush.net Removal Guide
Removing Fedapush.net requires a systematic approach to eliminate all traces of the malware from the infected system. Follow these steps carefully:
- Disconnect from the Internet: Disable all network connections to prevent further communication with the malware’s command and control servers.
- Enter Safe Mode: Restart your computer and press the appropriate key (usually F8 or Shift + F8) to enter Safe Mode.
- Uninstall Suspicious Programs: Go to Control Panel > Programs > Uninstall a Program, and uninstall any suspicious or unfamiliar programs.
- Delete Temporary Files: Use the Disk Cleanup utility to remove temporary files and other unnecessary data.
- Scan and Remove Malware: Use a reputable antivirus or antimalware program to scan your system and remove any detected threats, including Fedapush.net.
- Reset Browsers: Reset all installed browsers to default settings to remove any unwanted extensions or settings added by the malware.
- Restore System Settings: Use System Restore to revert your system to a previous state before the malware infection occurred.
Prevention Tips
To prevent future infections and protect your system from malware attacks, consider implementing the following best practices:
- Keep your operating system and software up-to-date with the latest security patches and updates.
- Exercise caution when downloading and installing software from the Internet, especially from untrusted sources.
- Enable real-time scanning and automatic updates for your antivirus or antimalware software.
- Use a firewall to monitor and control incoming and outgoing network traffic.
- Be vigilant against phishing attempts and avoid clicking on suspicious links or opening email attachments from unknown senders.
By following these proactive measures, you can fortify your defenses against Fedapush.net and other emerging cyber threats, ensuring the security and integrity of your digital assets.