Kixtixcy ransomware, a new strain of the notorious Dharma ransomware family, is a sophisticated threat designed to encrypt files, rename them, and extort victims for ransom payments. Discovered through VirusTotal sample submissions, Kixtixcy represents a dangerous evolution in ransomware tactics, targeting both local and network-shared files while employing advanced techniques to evade recovery methods.
What is Kixtixcy Ransomware?
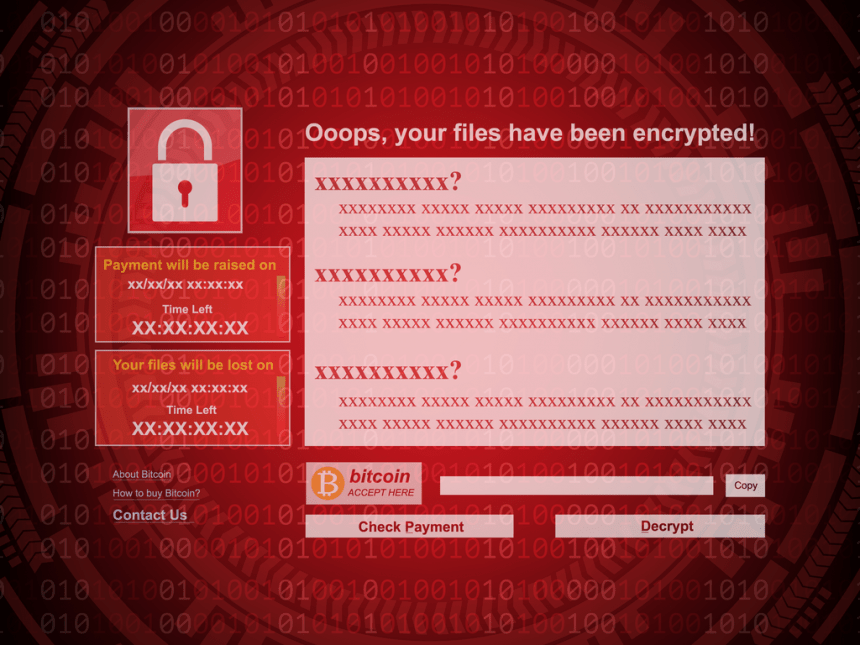
Kixtixcy ransomware encrypts files and modifies filenames by appending the victim’s unique ID, the attacker’s email address, and the “.kix” extension. For example, files like “1.jpg” and “2.png” are renamed to “1.jpg.id-9ECFA84E.[kixtixcy@tuta.io].kix” and “2.png.id-9ECFA84E.[kixtixcy@tuta.io].kix,” respectively. Additionally, Kixtixcy provides ransom notes through two channels: a text file (“kix_info.txt”) and a pop-up window.
Download SpyHunter Now & Scan Your Computer For Free!
Remove this and any other malicious threats to your system by scanning your computer with SpyHunter now! It’s FREE!
Ransom Note Overview
The ransom notes urge victims to contact the attackers via email (kixtixcy@tuta.io or kixtixcy@cyberfear.com) and provide a unique ID for file decryption. The notes warn victims to avoid using third-party decryption tools and offer an alternate contact if there is no response within 24 hours.
Technical Details
- Encryption and File Renaming:
- Encrypts files and changes extensions to “.kix.”
- Appends victim-specific details and attacker’s contact email to filenames.
- Persistence Mechanisms:
- Copies itself to the %LOCALAPPDATA% directory.
- Registers with Run keys to enable execution upon system startup.
- Recovery Prevention:
- Disables system firewalls.
- Deletes Volume Shadow Copies, thwarting common recovery methods.
- Targeting and Evasion:
- Likely avoids predetermined geographic regions.
- May collect location data.
How Does Kixtixcy Infect Systems?
Kixtixcy, like other Dharma family ransomware, uses multiple attack vectors:
- Vulnerable RDP Services: Exploits weak credentials through brute-force attacks.
- Phishing Emails: Malicious attachments or links containing macros.
- Software Vulnerabilities: Exploits unpatched systems.
- Malicious Downloads: Cracked software, P2P networks, or deceptive websites.
- Infected USB Drives and Ads: Spreads through removable media and malicious advertisements.
Consequences of Infection
Once Kixtixcy infects a system, the following occur:
- File Encryption: Critical data becomes inaccessible.
- Ransom Demand: Payment is required for file recovery.
- Potential Data Theft: Additional malware may steal sensitive data.
How to Remove Kixtixcy Ransomware
Download SpyHunter Now & Scan Your Computer For Free!
Remove this and any other malicious threats to your system by scanning your computer with SpyHunter now! It’s FREE!
Step 1: Isolate the Infected Device
Disconnect the device from the internet and any network connections to prevent further spread.
Step 2: Boot in Safe Mode
- Restart the computer.
- Press F8 or Shift + Restart during boot.
- Select “Safe Mode with Networking” from the menu.
Step 3: Use SpyHunter Anti-Malware Tool
SpyHunter is a reliable anti-malware tool designed to detect and remove ransomware and other malicious programs.
- Download and install SpyHunter.
- Launch the program and perform a full system scan.
- Follow the prompts to remove Kixtixcy ransomware and any associated threats.
Step 4: Restore Files
- Check Backups: Use backups to recover encrypted files.
- Data Recovery Tools: Tools like R-Studio or PhotoRec may recover some files.
- Contact Professionals: If necessary, consult data recovery experts.
Note: Avoid paying the ransom, as it does not guarantee file recovery and encourages criminal activities.
Preventing Future Infections
- Strengthen RDP Security:
- Use strong, unique passwords.
- Disable RDP if unnecessary.
- Restrict access to trusted IP addresses.
- Implement Regular Updates: Update operating systems, software, and antivirus tools to patch vulnerabilities.
- Educate Users: Train employees to recognize phishing emails and malicious attachments.
- Back Up Data: Maintain regular offline and cloud backups. Test backup integrity periodically.
- Use Comprehensive Security Solutions: Employ firewalls, intrusion detection systems, and anti-malware tools.
Conclusion
Kixtixcy ransomware is a severe threat capable of causing significant data loss and operational disruption. Its advanced encryption, persistence mechanisms, and targeting capabilities make it a formidable adversary. However, by following the outlined removal guide and implementing robust preventive measures, victims can mitigate the impact of this ransomware and protect their systems against future infections.