In the fast-paced world of cryptocurrency, where promises of quick profits and free digital assets abound, there lurks a sinister threat known as Cbusy. This deceptive platform, masquerading as a gateway to financial gain, is in reality a hotbed of scams and cybercriminal activity. Cbusy employs a cunning strategy, enticing unsuspecting individuals with the allure of free cryptocurrency giveaways and lucrative profits. However, beneath its facade of generosity lies a treacherous trap, designed to ensnare victims in a web of deceit and exploitation.
Actions and Consequences
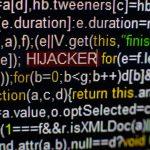
Cbusy operates on the premise of false promises and fraudulent schemes. It employs aggressive tactics, flooding social media channels with enticing offers of free digital currency and substantial returns on investments. The platform preys on the uninformed and the inexperienced, luring them into its clutches with the allure of easy money. However, behind the veil of generosity lies a malicious agenda. Cbusy utilizes Trojans—hidden dangers embedded within its messages—to infiltrate unsuspecting users’ devices. Once inside, these Trojans unleash havoc, stealing personal information and hijacking the device’s computing power to mine cryptocurrencies for the benefit of the scammers.
The consequences of falling victim to Cbusy are dire. Not only do individuals risk financial loss, but they also compromise their personal security. The theft of sensitive information can lead to identity theft, financial fraud, and a myriad of other cybercrimes. Moreover, the hijacking of computing resources can degrade device performance, compromising its functionality and leaving users vulnerable to further exploitation.
Cbusy operates under various aliases and is part of a larger network of cryptocurrency scams. Detection names for the malware associated with Cbusy may include Trojan.Cbusy, Trojan.Cryptominer, or similar variants. Similar threats in the realm of cryptocurrency scams include X Token Presale, Somezex, OGONTO, and others. These scams share common traits and tactics, indicating a coordinated effort by cybercriminals to defraud unsuspecting victims.
Removal Guide
If you suspect your device has been compromised by Cbusy or similar malware, it’s imperative to take immediate action to mitigate the threat. Follow these steps to remove the infection:
- Disconnect from the Internet: Safeguard your device by disconnecting it from the internet to prevent further communication with the malicious servers.
- Enter Safe Mode: Restart your device and enter Safe Mode to limit the malware’s ability to operate.
- Identify Malicious Processes: Use Task Manager (Windows) or Activity Monitor (Mac) to identify and terminate any suspicious processes associated with the malware.
- Delete Temporary Files: Clear temporary files and cache to remove any remnants of the malware’s presence on your device.
- Uninstall Suspicious Programs: Review your list of installed programs and uninstall any applications that are unfamiliar or suspicious.
- Update Security Software: Ensure your antivirus and antimalware software is up-to-date and run a full system scan to detect and remove any remaining threats.
- Reset Browser Settings: Reset your web browser to default settings to remove any malicious extensions or plugins installed by the malware.
- Change Passwords: As a precautionary measure, change passwords for sensitive accounts to prevent unauthorized access.
Best Practices for Prevention
Preventing future infections requires vigilance and proactive measures. Adopt the following best practices to safeguard against cryptocurrency scams and malware threats:
- Exercise Caution Online: Be wary of unsolicited messages, especially those promising free cryptocurrency or unrealistic profits.
- Research Before Investing: Conduct thorough research on cryptocurrency platforms and investment opportunities before committing any funds.
- Verify Sources: Verify the legitimacy of websites and individuals promoting cryptocurrency giveaways or investment schemes.
- Keep Software Updated: Regularly update your operating system, antivirus software, and web browsers to patch vulnerabilities and defend against malware.
- Use Strong Passwords: Create strong, unique passwords for each online account and enable two-factor authentication where available.
- Educate Yourself: Stay informed about the latest cybersecurity threats and scams, empowering yourself to recognize and avoid potential risks.
Conclusion
In the digital landscape rife with opportunities and pitfalls, Cbusy stands as a stark reminder of the dangers lurking beneath the surface. Its deceptive tactics and malicious intent pose a significant threat to individuals’ financial security and personal privacy. By remaining vigilant, informed, and proactive, users can protect themselves against the perils of cryptocurrency scams and malware attacks, safeguarding both their assets and their identity from exploitation.